Ransomware identified as the fastest growing malware threat
Bernard Collin, CEO of SafeComs Network Security
What is ransomware?
Ransomware is a type of malware that encrypts files on a targeted system or network. Once the targeted files are encrypted, the ransomware demands payment in exchange for providing a key to decrypt the files, often around $1,000 – $20,000 in Bitcoins. We’ve seen cases where as much as $5M was paid to the attackers. Most ransomware variants opportunistically target victims. They can infect a wide array of devices from computers to smartphones. Any networked device could potentially be affected by ransomware.
It’s important to know that paying the ransom never guarantees that the decryption key will be received, or that the encrypted files will be restored.
How do you get ransomware?
Most ransomware is unintentionally downloaded by clicking on a malicious link, often in a spam email. It’s also possible to pick up ransomware during a visit to a malicious or compromised website by way of drive-by downloads, which don’t require user engagement for the infection to be successful.
Occasionally ransomware is the result of brute force attacks carried out by way of the Remote Desktop application, which is becoming increasingly popular as the working population works from home.
It’s easy to imagine just one person in your organisation accidentally clicking on a malicious link or falling victim to an attack. With just one compromised employee, your entire network could be in jeopardy.
Early ransomware infections were typically opportunistic attacks against random targets. Today ransomware is often deployed as part of a targeted campaign with specific victims in mind. Malicious links and spam emails will be tailored to the unique professional situation of the intended target, and will usually contain material related to a plausible activity (i.e. “here is your budget for revision, please approve…” or, “here is the link to our company outing with all our photos, feel free to share with your friends…”).
A developing trend
A growing trend with PDPA and the “Working from Home” Covid campaign is the additional capability of data exfiltration. If a victim doesn’t pay the ransom, their files may end up being published on a publicly exposed server, for all to see.
In addition to the embarrassment, there’s also a profoundly serious business risk due to the loss of confidentiality amongst clients and the potential of heavy fines incurred under the governance of PDPA.
To make matters worse, ransomware today doesn’t require technical expertise. Malicious actors can simply use a RaaS (Ransomware as a service) application, which allows them to rent the malware along with technical support and tutorial features, and simply share some portion of the loot with the ransomware’s creator after the fact.
This level of accessibility and ease of use makes ransomware a particularly worrisome threat.
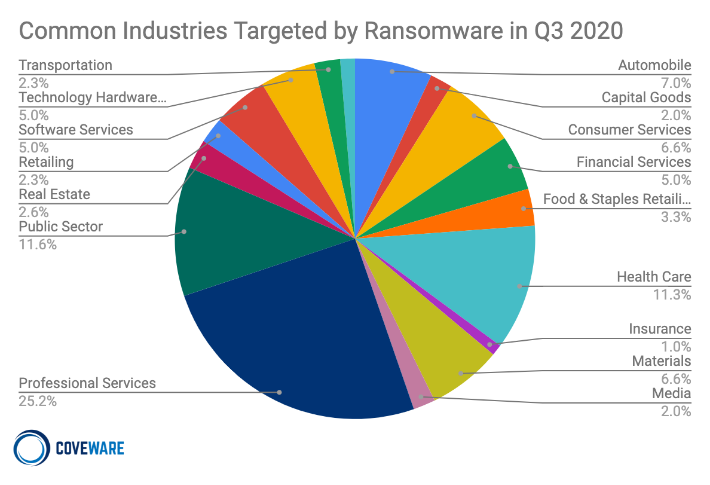
Who is a target?
The largest companies were the initial targets; however, their technical capability makes them harder to penetrate. Now we see a move towards smaller entities in the service industry, where costs rarely allow for a full-time IT team with security expertise. Most engineers would have a lower technical profile, enough to support business operations without any kind of subject specific security knowledge.
How to stay protected
At SafeComs we believe that SMEs deserve the best protection available at an affordable price, with expertise similar to what was once reserved for large Enterprises. Our experts are available on an individual project or ongoing basis, with enough time to review the security status, evaluate the risks and put in place mechanisms and procedures to secure your company and its systems.
This is why we created a Cybersecurity Awareness training program, delivered online with a certificate of completion for each employee. We review security status and advise on best practices, in addition to testing the resistance of your company to emerging threats. We use sophisticated tools to block malware and the transfer of their encryption programs, developing and enforcing security policies aimed at protecting your enterprise from any angle.
How can I prepare for a ransomware attack?
The following elements are vital to creating a secure environment for the company and employees:
- An incident response plan that describes how to react to malware is paramount
- Your backups are critical. Not on a network disk, not onsite, encrypted and with a daily history.
- Up to date antivirus, anti-phishing, Security patches, SPAM filter and a policy to block encrypted files, an important vector of malware today.
- Monitor your internet traffic and limit access to sites not required for your activity.
- Segregate data with privileges elevation, not everybody needs access to everything
- Control and approve the third party who can access your network
- Have a mechanism to record and report incidents
Bernard Collin is the CEO of SafeComs Network Security. SafeComs monitors PCs and Servers across South East Asia with a unique proprietary tool, Total Control. Headquartered in Thailand, SafeComs supports a large network of prestigious SMEs in the region and delivers quality security solutions to their clients. SafeComs is responsible for the security of systems and data of HLB Thailand.